The Specter of Post-Quantum Causality: Rethinking Security in a Universe Beyond Quantum Mechanics
For decades, the burgeoning field of quantum computing has cast a long shadow over the digital world, with researchers understanding that these powerful machines will eventually possess the capability to shatter the cryptographic codes that safeguard vast swathes of our online existence. In response, a parallel effort has been underway for years, dedicated to developing a new generation of "quantum-resistant" or "post-quantum" cryptography, designed to withstand the onslaught of future quantum safecrackers. Concurrently, scientists have been harnessing the peculiar rules of quantum mechanics itself to forge entirely new paradigms for secure communication. However, a profound question now looms: what happens if the very theoretical framework upon which these quantum communication techniques are built—quantum mechanics—is itself superseded by a more fundamental theory, much as quantum mechanics supplanted Newtonian physics a century ago? Will these sophisticated quantum protocols remain secure in a universe governed by an even deeper set of natural laws?
"In terms of these cryptographic protocols, it’s good to be paranoid," states Ravishankar Ramanathan, a quantum information theorist at the University of Hong Kong, whose research focuses on quantum cryptography. "Let’s try to minimize the assumptions behind the protocol. Let’s suppose that at some future date people realize that quantum mechanics is not the ultimate theory of nature." This sentiment underscores a growing awareness within the scientific community that even the most advanced current theories may not represent the final word on the universe’s mechanics. The persistent difficulties in reconciling quantum mechanics with general relativity, particularly in the quest for a unified theory of quantum gravity, suggest that any successor theory might indeed involve principles that are currently unimaginable.
This contemplation of the unknown has led some quantum cryptographers to seek even more foundational principles upon which to build their security measures. Rather than anchoring their work solely in the tenets of quantum mechanics, they are delving deeper, exploring the very concept of causality—the relationship between cause and effect—as a more robust bedrock for future security.
The Subtle Art of Quantum Jamming
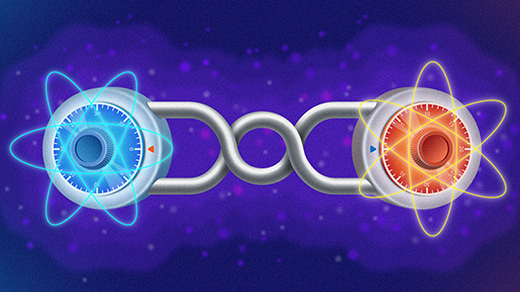
One illustrative way to grasp these complex developments is through the lens of quantum key distribution (QKD). This technology leverages the principles of quantum mechanics to securely transmit a cryptographic key—an essential component for decoding secret messages—in a manner that is inherently resistant to covert tampering. At its core, QKD often relies on quantum entanglement, a phenomenon where two particles become intrinsically linked, sharing correlated properties even when separated by vast distances. This entanglement acts as a kind of "tripwire." Should an eavesdropper attempt to intercept or manipulate the entangled particles to steal the key, the very act of intrusion would disrupt the delicate entanglement, thereby revealing the sabotage. This protective mechanism is deeply rooted in a fundamental quantum mechanical principle known as the "monogamy of entanglement."
The monogamy of entanglement dictates that if two particles are maximally entangled with each other, neither can be entangled with a third particle. This property ensures that an observer measuring one particle gains complete information about the other, and crucially, that no third party can interfere without being detected. However, the unsettling question arises: what if this principle, so central to current quantum security, were to falter? In such a hypothetical scenario, if the parties involved in a QKD protocol did not possess absolute control over their quantum devices, an external agent could potentially subtly alter the entanglement between particles without leaving any overt trace. This insidious act is termed "quantum jamming."
The study and understanding of quantum jamming have surged in recent years, fueled by its potential to illuminate both the intricacies of quantum mechanics and the fundamental nature of cause and effect. Researchers are grappling with a critical question: are there inherent, deep-seated principles that categorically forbid jamming, rendering it impossible? Or, if no such principle exists, could jamming indeed manifest in the physical world, posing a threat to our current understanding of secure communication?
"Jim the Jammer": A Thought Experiment in Causality
To conceptualize the phenomenon of quantum jamming, theoretical physicist Michaël Eckstein of Jagiellonian University in Krakow, Poland, often employs a narrative analogy featuring the archetypal characters of quantum mechanics, Alice and Bob.
"Suppose you have Alice and Bob, and they meet a magician, Jim the Jammer," Eckstein explains. "The magician says, ‘I have two balls; one is white, and one is black.’"
These balls represent a pair of entangled particles. In quantum entanglement, particles share a linked property; for instance, if one particle is measured to have "spin up," the other will invariably exhibit "spin down," irrespective of their spatial separation. In Eckstein’s analogy, the balls are linked such that if one is white, the other must be black.
Following a classic magician’s trope, Jim allows audience members to witness the balls being placed into two separate boxes, thoroughly mixed, and then handed to Alice and Bob. At this stage, the identity of the ball within each box remains unknown to everyone.
Subsequently, Alice and Bob embark on journeys in rocket ships, accelerating to speeds approaching the velocity of light in opposite directions. After a period of travel, they independently open their respective boxes. Crucially, during their journeys, Jim the Jammer performs a subtle trick, altering the entangled state of the balls.
Initially, neither Alice nor Bob detects any anomaly. Each anticipates a 50% probability of finding either a white or black ball, and upon opening their boxes, they find just that—a white or black ball. At this point, Jim’s actions seem to have had no observable effect on their individual outcomes.
The magician’s trick, however, is revealed when Alice and Bob reconvene on Earth and compare their observations. They discover that their balls are not opposite colors as expected from a standard entangled state, but rather, they are the same color. Jim has effectively manipulated the balls’ entanglement, transforming it from a state of perfect anticorrelation (one white, one black) to one of perfect correlation (both white or both black). This, in essence, illustrates the core concept of quantum jamming, though the actual quantum mechanical process is more nuanced.
The Genesis of Jamming and the No-Signaling Principle
The theoretical groundwork for exploring phenomena like quantum jamming was laid in the mid-1990s by Jacob Grunhaus, Sandu Popescu, and Daniel Rohrlich. Their research explored the boundaries of theories that might extend beyond quantum mechanics while still adhering to a fundamental tenet of Albert Einstein’s theory of relativity: the principle that information cannot travel faster than the speed of light. Einstein’s thought experiments had demonstrated that without this "no-signaling" principle, the very fabric of causality—the predictable sequence of cause and effect—would begin to unravel. Consequently, the no-signaling principle has become a cornerstone assumption for physicists contemplating theories that might transcend quantum mechanics. "When we work in quantum foundations, what we take very seriously is the no-signaling principle," affirms Mirjam Weilenmann of the French national research institute Inria.
Grunhaus, Popescu, and Rohrlich conceptualized jamming as a form of "super-entanglement" that could interfere with pre-existing entangled particle pairs. Their model suggested that just as a measurement device can determine the state of a distant entangled particle, a hypothetical jamming device could alter the correlations between two distant entangled particles. If this jamming process adhered to a specific set of rules, some physicists argue, it could clandestinely disrupt quantum entanglement without violating causality or the no-signaling principle.
The implications of this theoretical construct were so profound and counterintuitive that, upon its publication, it garnered limited immediate attention. "We wrote that paper and that was the end of it," recalls Sandu Popescu.
A Resurgence of Interest in a Post-Quantum World
It took approximately two decades for the theoretical seeds sown by Grunhaus, Popescu, and Rohrlich to germinate into a field of active research. The intervening years witnessed the maturation of quantum computing from a theoretical curiosity into tangible experimental systems. This period, particularly the first decade of the 2000s, also saw the development of "device-independent" quantum key distribution protocols by several research groups. These advanced QKD techniques crucially depend on the monogamy of entanglement to guarantee security, a reliance that would be fatally undermined by the possibility of quantum jamming.
In 2016, while contemplating these device-independent protocols, Ramanathan and Paweł Horodecki revisited the 1990s paper on jamming. "We started to realize that this property of monogamy, upon which all of device-independent cryptography is based, completely fails once you start to allow these types of jamming correlations," Ramanathan stated. This realization ignited a flurry of debate and research within the quantum information community.
Many researchers found the concept of quantum jamming deeply unsettling. While it might not permit faster-than-light signaling, the ability to influence the state of a distant quantum particle still evoked the "spooky action at a distance" that had troubled Einstein. This perceived violation of intuitive causality, even if mathematically consistent with no-signaling, prompted a search for deeper underlying principles.
Causality Under Scrutiny: The Quest for New Principles
For some researchers, however, the very discomfort generated by quantum jamming has proven to be a fertile ground for new theoretical insights. "I see it as a tool to try to help hone our intuitions of what the right definition of causation is," says Roger Colbeck, who proposed one of the earliest device-independent cryptography protocols in his 2006 doctoral thesis. Now at King’s College London, Colbeck, in collaboration with V. Vilasini at the Inria research center in Grenoble Alpes, is engaged in classifying the ways cause and effect operate across different theoretical frameworks. For them, jamming serves as a critical "edge case"—a scenario that tests the limits of our understanding. Their work aims to identify fundamental principles, akin to the no-signaling principle, that could delineate the boundaries of phenomena like quantum jamming.
Responding to this research, as well as a recent paper by Weilenmann, groups led by Ramanathan and Horodecki, in collaboration with Eckstein, Tomasz Miller, and Paweł Horodecki’s father, Ryszard Horodecki, published a preprint in December 2025. This collective effort aims to clarify terminology, resolve misunderstandings, and collectively search for the more fundamental principles that underpin all physical theories, including those that might supersede quantum mechanics.
"That’s for me the most interesting question," Eckstein muses. "Is there any new physics behind it? Can physics include such phenomena?" The ongoing dialogue among these researchers underscores the profound implications of quantum jamming, pushing the boundaries of our comprehension of quantum mechanics, causality, and the ultimate nature of physical reality. The quest to understand these phenomena is not merely an academic exercise; it is a crucial step in ensuring the long-term security of our digital future in a universe that may yet hold surprises far beyond our current theoretical grasp. The implications extend beyond cryptography, touching upon our deepest understanding of how the universe works and the very nature of reality itself. The potential for phenomena that operate at the very edge of our current physical laws necessitates a constant re-evaluation of our foundational assumptions, ensuring that our scientific models remain robust and adaptable to the unfolding mysteries of the cosmos.